What is Cloud Computing?
Cloud computing is defined as a type of computing that relies on sharing computing resources rather than having local servers or personal devices to handle applications. Cloud computing allows consumers and businesses to use applications without installation and access their personal files on any computer with internet access. This technology allows for much more efficient computing by centralizing data storage, processing, and bandwidth. A simple example of cloud computing is Yahoo email, Gmail, Hotmail, etc.
What cloud computing is not about is your hard drive. When you store data on or run programs from the hard drive, that’s called local storage and computing. Everything you need is physically close to you, which means accessing your data is fast and easy, for that one computer, or others on the local network. Working off your hard drive is how the computer industry functioned for decades; some would argue it’s still superior to cloud computing.
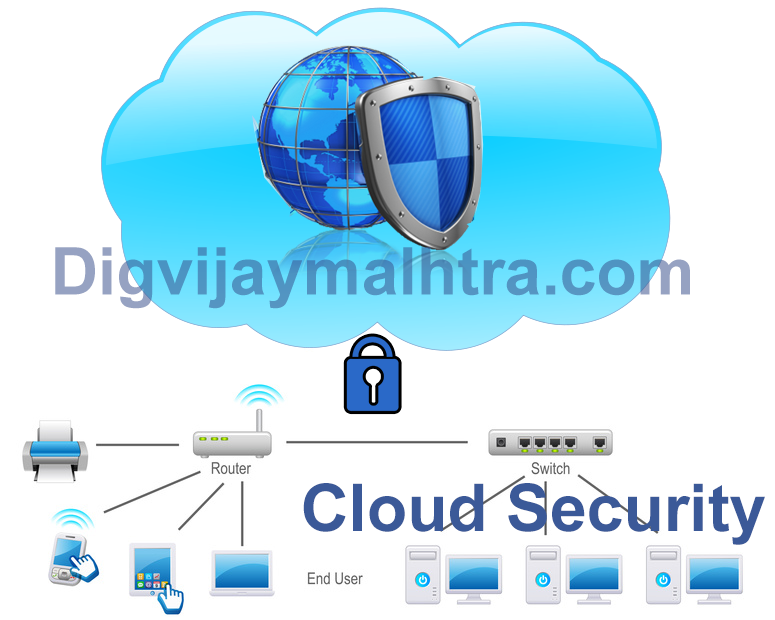
Cloud Security Guidance
As consumers transition their applications and data to use cloud computing, it is critically important that
the level of security provided in the cloud environment be equal to or better than the security provided
by their traditional IT environment. Failure to ensure appropriate security protection could ultimately
result in higher costs and potential loss of business thus eliminating any of the potential benefits of
cloud computing.
This section provides a prescriptive series of steps that should be taken by cloud consumers to evaluate
and manage the security of their cloud environment with the goal of mitigating risk and delivering an
the appropriate level of support. The following steps are discussed in detail:
- Ensure effective governance, risk, and compliance processes exist
- Audit operational and business processes
- Manage people, roles, and identities
- Ensure proper protection of data and information
- Enforce privacy policies
- Assess the security provisions for cloud applications
- Ensure cloud networks and connections are secure
- Evaluate security controls on physical infrastructure and facilities
- Manage security terms in the cloud SLA
- Understand the security requirements of the exit process
-
Overcome common cloud security concerns and compliance obstacles by extending corporate security and policies to apply to cloud traffic.
-
Protect, identify, and classify all critical data while it moves between the enterprise and the cloud.
-
Combine data loss prevention, email, web, identity, and access management under a single, modular-based platform. We offer flexible deployment options, including on-premises, cloud, or a hybrid of both.
-
Take advantage of the increased scalability, flexibility, availability, and lower costs offered by the cloud, while carefully monitoring data to make sure it is protected.
We Provide Services In the Following Cities
Ethical Haker in Ludhiana
Ethical Hacking Services in Amritsar
Ethical Hacking Services in Mumbai
Ethical Hacking Services in Delhi
*Ethical Hacking Services in Gujarat
Ethical Hacking Services in Chandigarh