Hacking Facebook Accounts with just a phone number through the SS7 protocol

Hacking Facebook Accounts with just a phone number is possible, experts from Positive Technologies demonstrated it by exploiting flaws in the SS7 protocol.
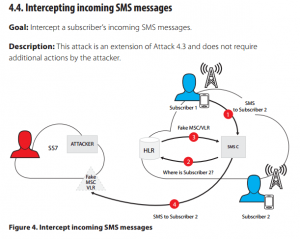
Hacking Facebook accounts by knowing phone numbers is possible, a group of researchers from Positive Technologies demonstrated it.“Researchers have proven just that by taking control of a Facebook account with only a phone number and some hacking skills to exploit the SS7 network, a core piece of telecoms infrastructure shown to be vulnerable repeatedly over the last half decade.” reported a blog post published on Forbes. The security issue in the SS7 signaling system could be exploited by criminals, terrorists, and intelligence agencies to spy on communications. The SS7 protocol allows cell phone carriers to collect location data related to the user’s device from cell phone towers and share it with other carriers, this means that by exploiting the SS7 a carrier is able to discover the position of its customer everywhere he is.
The team of researchers from Positive Technologies is the same that recently demonstrated how to hack WhatsApp and Telegram accounts by leveraging the SS7 protocol.
The attack method devised by the experts from Positive Technologies works against any service that relies on SMS to verify user accounts, including Gmail and Twitter.
The Facebook hack takes the exploits a step further, only requiring a phone number. The attacker clicks on the “Forgot account?” link on the Facebook.com homepage. When asked for an email address or phone number linked to the target account, the hacker provides the legitimate number. By diverting the text message containing a one-time passcode to their own PC or phone, they can log in to the account, as shown in the video below.
What does SS7 normally do?
SS7 is a set of protocols allowing phone networks to exchange the information needed for passing calls and text messages between each other and to ensure correct billing. It also allows users on one network to roam on another, such as when traveling in a foreign country.
What can access to SS7 enable hackers to do?
Once they have access to the SS7 system, a hacker can essentially have access to the same amount of information and snooping capabilities as security services.
They can transparently forward calls, giving them the ability to record or listen in to them. They can also read SMS messages sent between phones, and track the location of a phone using the same system that the phone networks use to help keep a constant service available and deliver phone calls, texts, and data.
Who is affected by the vulnerability?
Should a hacker gain entry to the SS7 system on any number of networks, or if they are used by a law enforcement agency as part of its surveillance, anyone with a mobile phone could be vulnerable.
We Provide Services In the Following Cities
Ethical Hacker in Ludhiana
Ethical Hacking Services in Ludhiana
Ethical Hacking Services in Mumbai
Ethical Hacking Services in Delhi
Ethical Hacking Services in Gujarat
Ethical Hacking Services in Chandigarh