VPN Tunneling Protocols
Applies To: Windows Server 2008
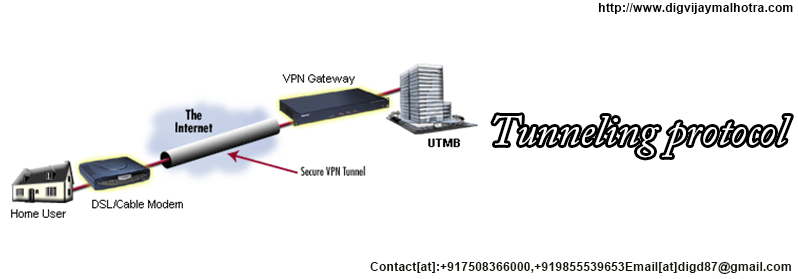
Tunneling enables the encapsulation of a packet from one type of protocol within the datagram of a different protocol. For example, VPN uses PPTP to encapsulate IP packets over a public network, such as the Internet. A VPN solution based on Point-to-Point Tunneling Protocol (PPTP), Layer Two Tunneling Protocol (L2TP), or Secure Socket Tunneling Protocol (SSTP) can be configured.
PPTP, L2TP, and SSTP depend heavily on the features originally specified for Point-to-Point Protocol (PPP). PPP was designed to send data across dial-up or dedicated point-to-point connections. For IP, PPP encapsulates IP packets within PPP frames and then transmits the encapsulated PPP packets across a point-to-point link. PPP was originally defined as the protocol to use between a dial-up client and a network access server.
PPTP
PPTP allows multiprotocol traffic to be encrypted and then encapsulated in an IP header to be sent across an IP network or a public IP network, such as the Internet. PPTP can be used for remote access and site-to-site VPN connections. When using the Internet as the public network for VPN, the PPTP server is a PPTP-enabled VPN server with one interface on the Internet and a second interface on the intranet.
Encapsulation
PPTP encapsulates PPP frames in IP datagrams for transmission over the network. PPTP uses a TCP connection for tunnel management and a modified version of Generic Routing Encapsulation (GRE) to encapsulate PPP frames for tunneled data. The payloads of the encapsulated PPP frames can be encrypted, compressed, or both. The following figure shows the structure of a PPTP packet containing an IP datagram.
Encryption
The PPP frame is encrypted with Microsoft Point-to-Point Encryption (MPPE) by using encryption keys generated from the MS-CHAP v2 or EAP-TLS authentication process. Virtual private networking clients must use the MS-CHAP v2 or EAP-TLS authentication protocol in order for the payloads of PPP frames to be encrypted. PPTP is taking advantage of the underlying PPP encryption and encapsulating a previously encrypted PPP frame.
L2TP
L2TP allows multiprotocol traffic to be encrypted and then sent over any medium that supports point-to-point datagram delivery, such as IP or asynchronous transfer mode (ATM). L2TP is a combination of PPTP and Layer 2 Forwarding (L2F), a technology developed by Cisco Systems, Inc. L2TP represents the best features of PPTP and L2F.
Unlike PPTP, the Microsoft implementation of L2TP does not use MPPE to encrypt PPP datagrams. L2TP relies on Internet Protocol security (IPsec) in Transport Mode for encryption services. The combination of L2TP and IPsec is known as L2TP/IPsec.
Both L2TP and IPsec must be supported by both the VPN client and the VPN server. Client support for L2TP is built into the Windows Vista® and Windows XP remote access clients, and VPN server support for L2TP is built into members of the Windows Server® 2008 and Windows Server 2003 family.
L2TP is installed with the TCP/IP protocol.
Encapsulation
Encapsulation for L2TP/IPsec packets consists of two layers:
First layer: L2TP encapsulation
A PPP frame (an IP datagram) is wrapped with an L2TP header and a UDP header.
Encryption
The L2TP message is encrypted with either Data Encryption Standard (DES) or Triple DES (3DES) by using encryption keys generated from the Internet Key Exchange (IKE) negotiation process.
SSTP
Secure Socket Tunneling Protocol (SSTP) is a new tunneling protocol that uses the HTTPS protocol over TCP port 443 to pass traffic through firewalls and Web proxies that might block PPTP and L2TP/IPsec traffic. SSTP provides a mechanism to encapsulate PPP traffic over the Secure Sockets Layer (SSL) channel of the HTTPS protocol. The use of PPP allows support for strong authentication methods, such as EAP-TLS. SSL provides transport-level security with enhanced key negotiation, encryption, and integrity checking.
When a client tries to establish an SSTP-based VPN connection, SSTP first establishes a bidirectional HTTPS layer with the SSTP server. Over this HTTPS layer, the protocol packets flow as the data payload.
Encapsulation
SSTP encapsulates PPP frames in IP datagrams for transmission over the network. SSTP uses a TCP connection (over port 443) for tunnel management as well as PPP data frames.
Encryption
The SSTP message is encrypted with the SSL channel of the HTTPS protocol.
Choosing between tunneling protocols
When choosing between PPTP, L2TP/IPsec, and SSTP remote access VPN solutions, consider the following:
- PPTP can be used with a variety of Microsoft clients including Microsoft Windows 2000, Windows XP, Windows Vista, and Windows Server 2008. Unlike L2TP/IPsec, PPTP does not require the use of public key infrastructure (PKI). By using encryption, PPTP-based VPN connections provide data confidentiality (captured packets cannot be interpreted without the encryption key). PPTP-based VPN connections, however, do not provide data integrity (proof that the data was not modified in transit) or data origin authentication (proof that the data was sent by the authorized user).
- L2TP can only be used with client computers running Windows 2000, Windows XP, or Windows Vista. L2TP supports either computer certificates or a preshared key as the authentication method for IPsec. Computer certificate authentication, the recommended authentication method, requires a PKI to issue computer certificates to the VPN server computer and all VPN client computers. By using IPsec, L2TP/IPsec VPN connections provide data confidentiality, data integrity, and data authentication. Unlike PPTP and SSTP, L2TP/IPsec enables machine authentication at the IPsec layer and user-level authentication at the PPP layer.
- SSTP can only be used with client computers running Windows Vista Service Pack 1 (SP1) or Windows Server 2008. By using SSL, SSTP VPN connections provide data confidentiality, data integrity, and data authentication.
- All three tunnel types carry PPP frames on top of the network protocol stack. Therefore, the common features of PPP, such as authentication schemes, Internet Protocol version 4 (IPv4) and Internet Protocol version 6 (IPV6) negotiation, and Network Access Protection (NAP), remain the same for the three tunnel types.
We Provide Services In the Following Cities
Ethical Haker in Ludhiana
Ethical Hacking Services in Ludhiana
Ethical Hacking Services in Mumbai
Ethical Hacking Services in Delhi
Ethical Hacking Services in Gujarat
Ethical Hacking Services in Chandigarh